Create an IAM Role
Time Estimate: 5 - 10 minutes
In this section you will create a suitable IAM role that will give the approriate execution priviliges to your S3 Processor Lambda function.
Make sure you are in N. Virginia region. Look for the Identity and Access Management (IAM) service in the AWS Management console and click on the highlighted result to access the service.
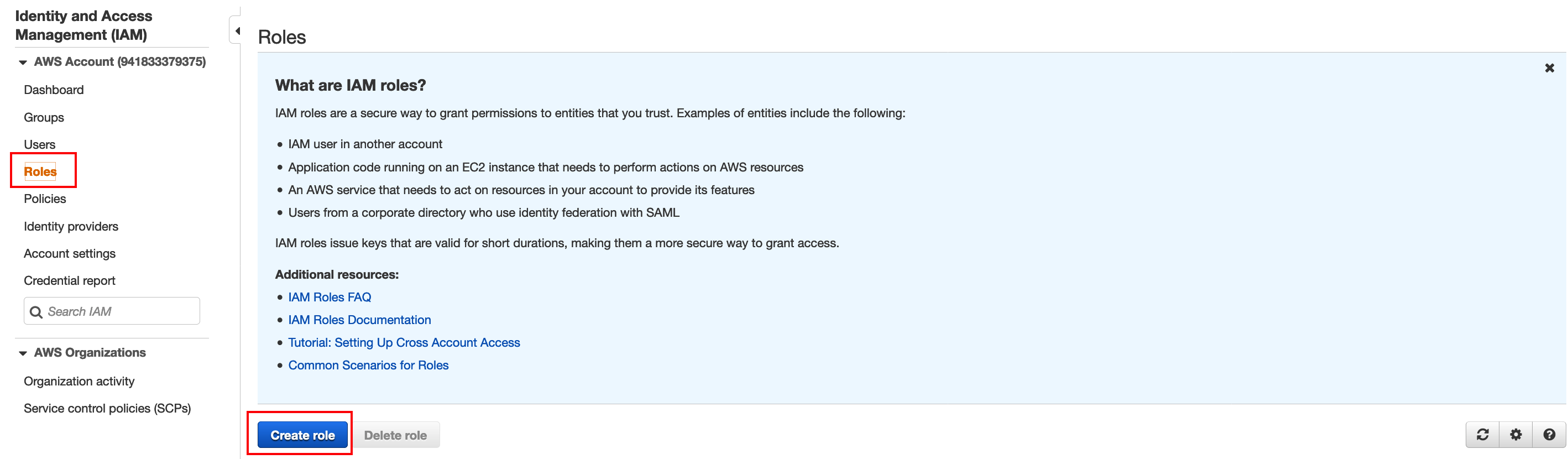
Once you have accessed the IAM service go to the Roles section as shown below and click Create role:
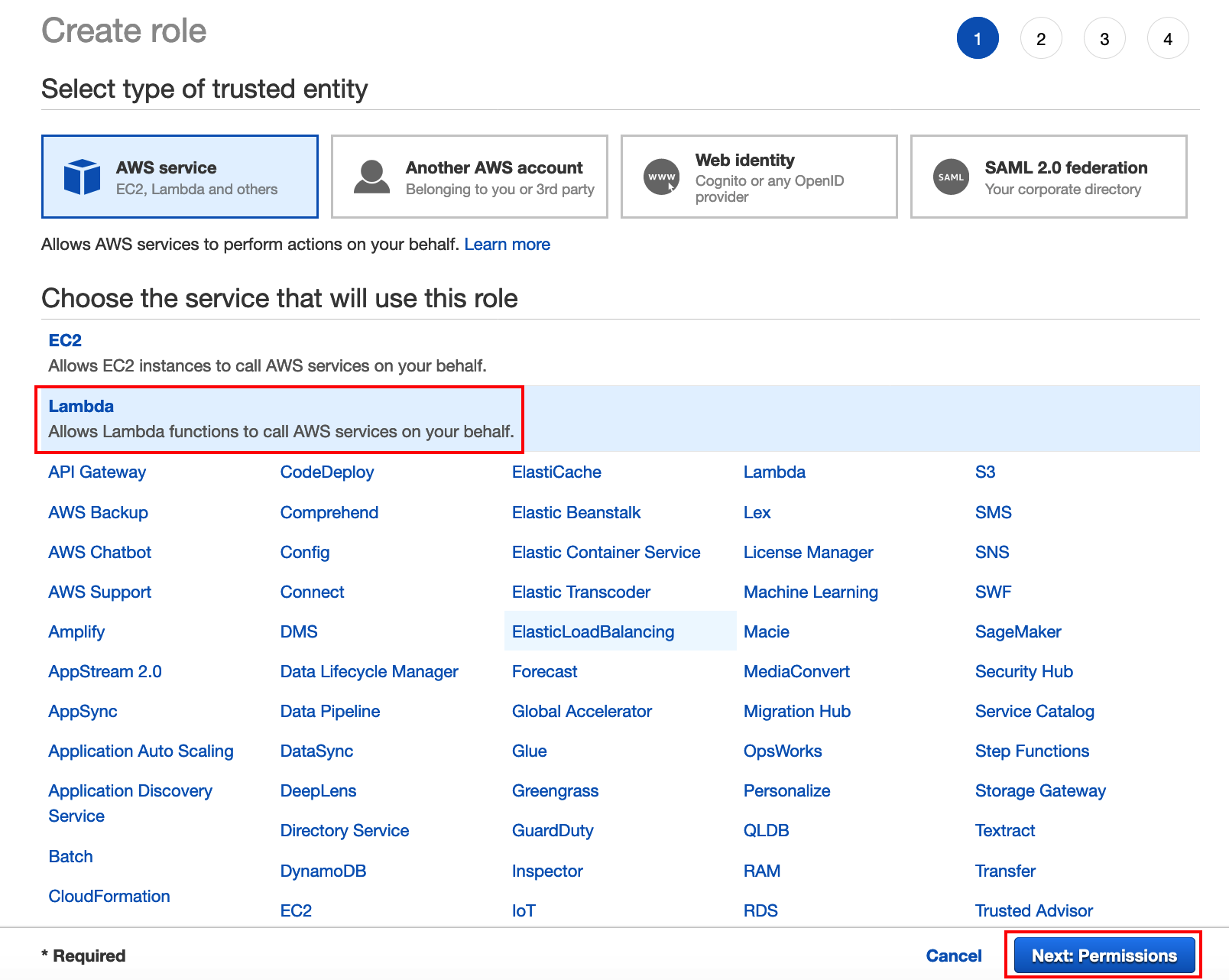
Select Lambda like below and click Next:Permissions:
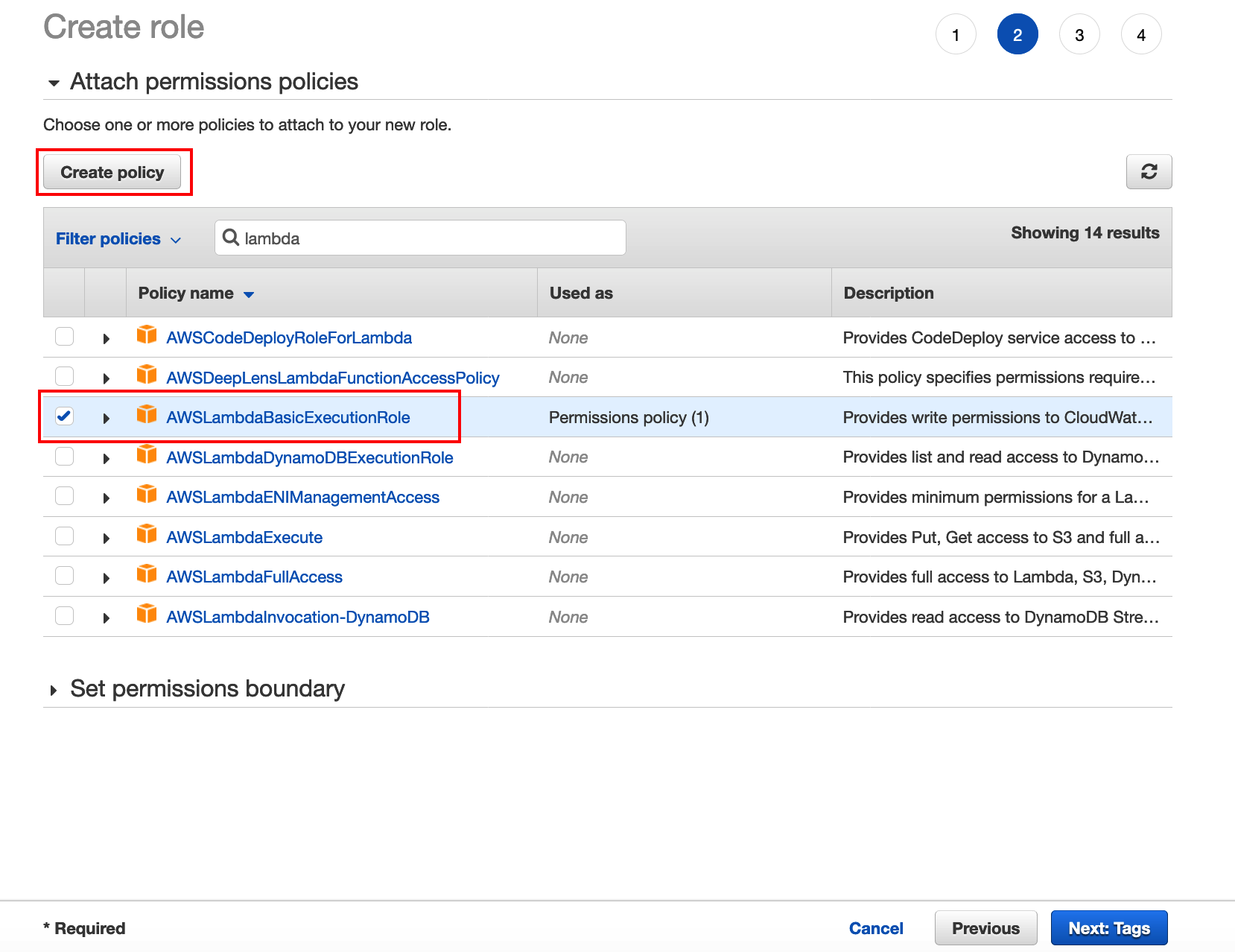
Select LambdaBasicExecutionPolicy and then select Create policy. This action should open a new tab where you can create the IAM policy.
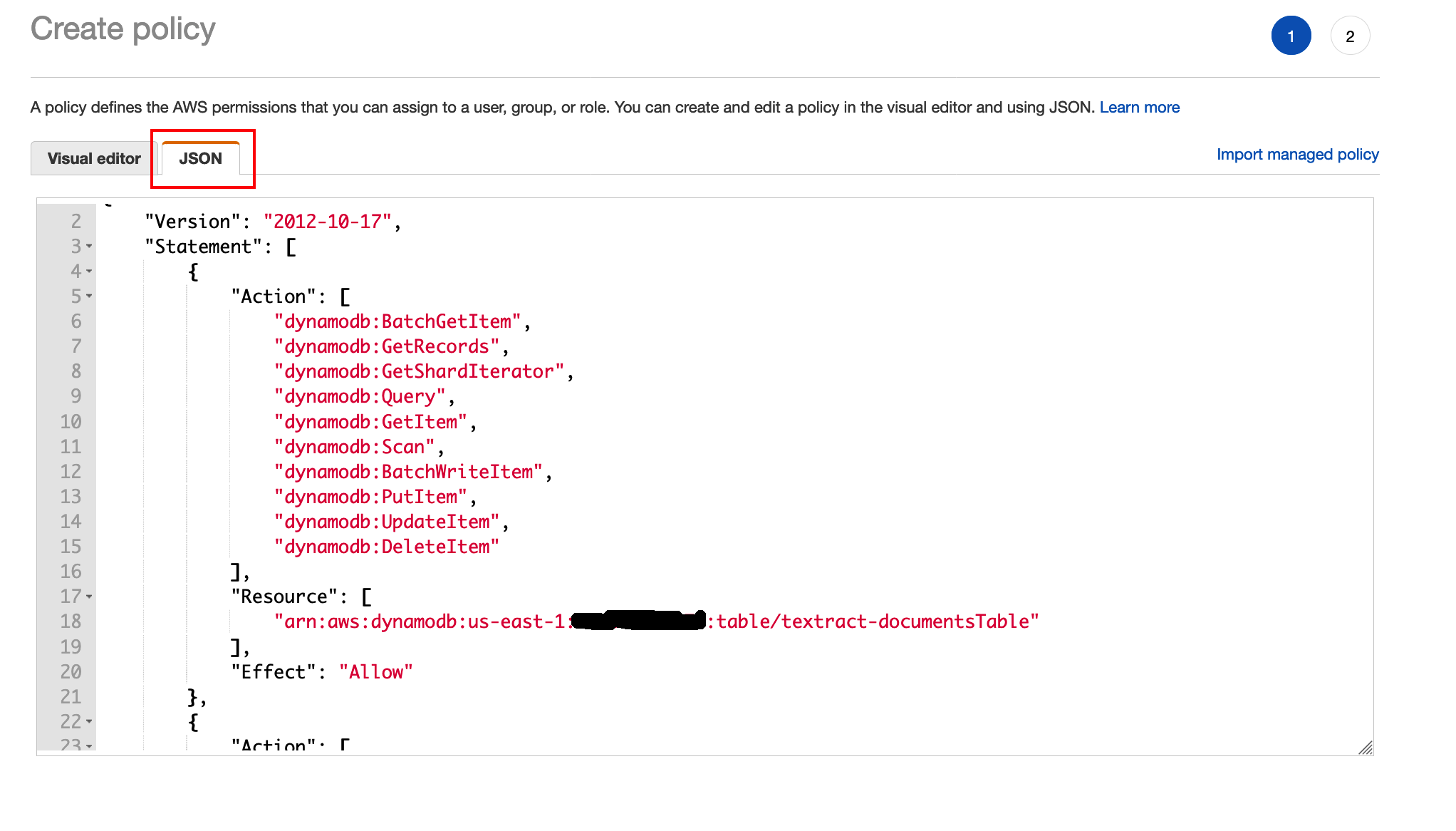
Copy the IAM policy below after populating your SQS and DynamoDB ARNs that you took a note of in previous steps
***(REPLACE WITH YOUR OWN DOCUMENTS TABLE ARN, REPLACE WITH YOUR OWN SQS ARN)***
{
"Version": "2012-10-17",
"Statement": [
{
"Action": [
"dynamodb:BatchGetItem",
"dynamodb:GetRecords",
"dynamodb:GetShardIterator",
"dynamodb:Query",
"dynamodb:GetItem",
"dynamodb:Scan",
"dynamodb:BatchWriteItem",
"dynamodb:PutItem",
"dynamodb:UpdateItem",
"dynamodb:DeleteItem"
],
"Resource": [
"REPLACE WITH YOUR OWN DOCUMENTS TABLE ARN"
],
"Effect": "Allow"
},
{
"Action": [
"sqs:SendMessage",
"sqs:SendMessageBatch",
"sqs:GetQueueAttributes",
"sqs:GetQueueUrl"
],
"Resource": "REPLACE WITH YOUR OWN SQS ARN",
"Effect": "Allow"
}
]
}Then paste the policy in the Json section as indicated below:
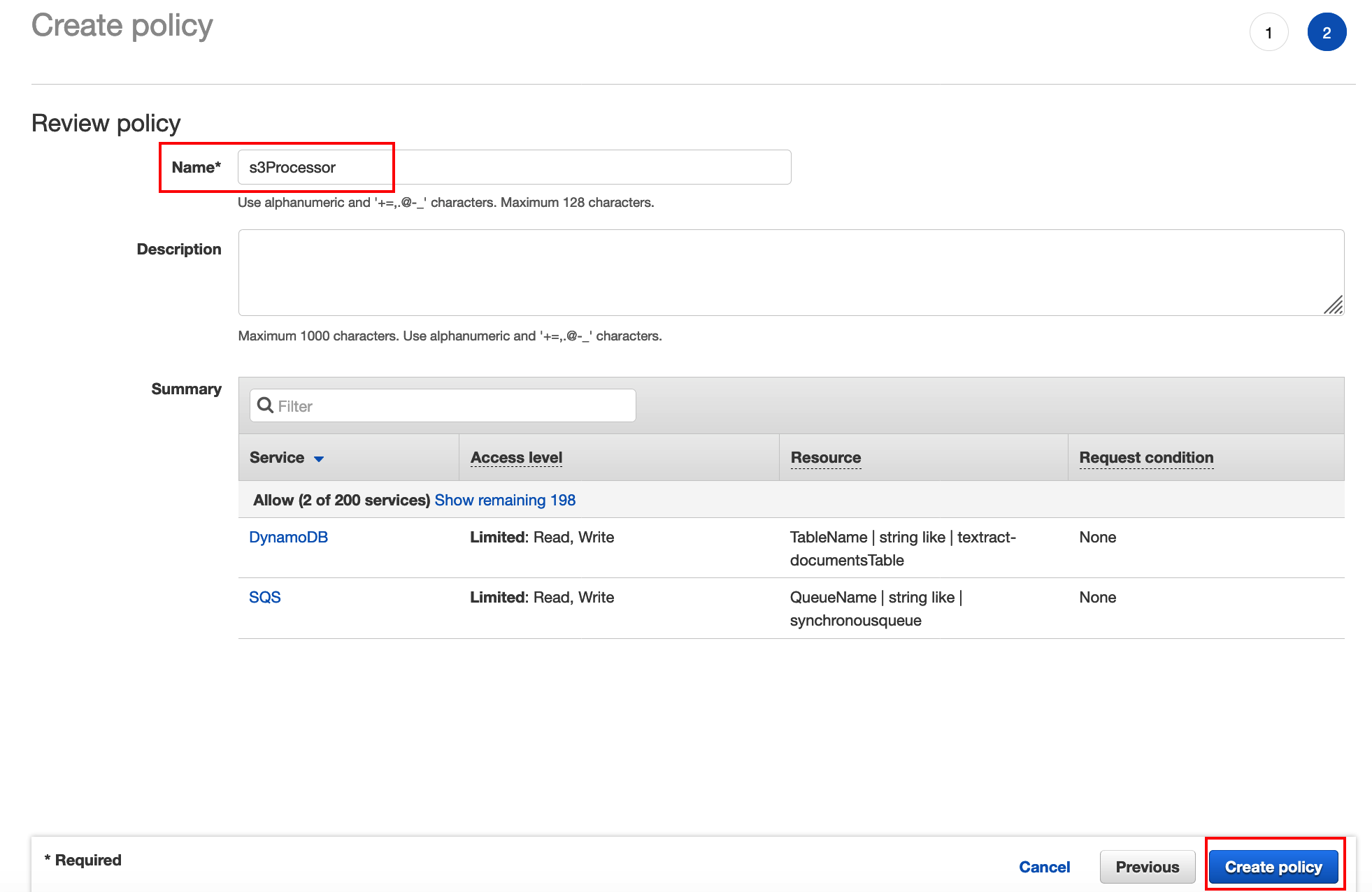
Click review policy and you should see the following screen. Give the policy a name like in the screeshot below and click Create policy.
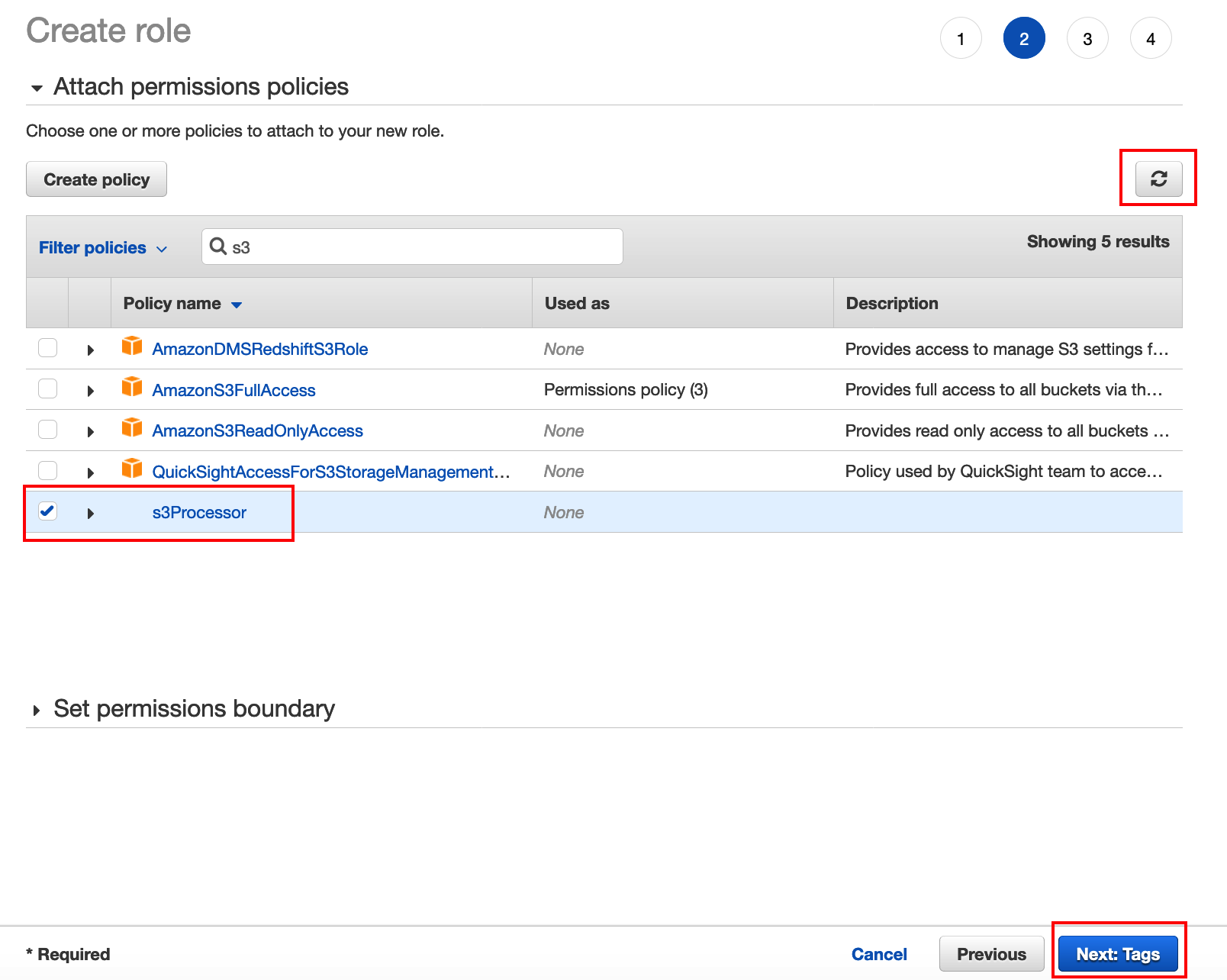
As soon as you create the IAM policy go back to your original tab to finish the creation of the IAM Role. Find the new policy you just created and attach this to your role. If the new policy does not appear in your search click the refresh button and search again. After you select the newly created policy click Next:tags
Click Next:review in the next screen.
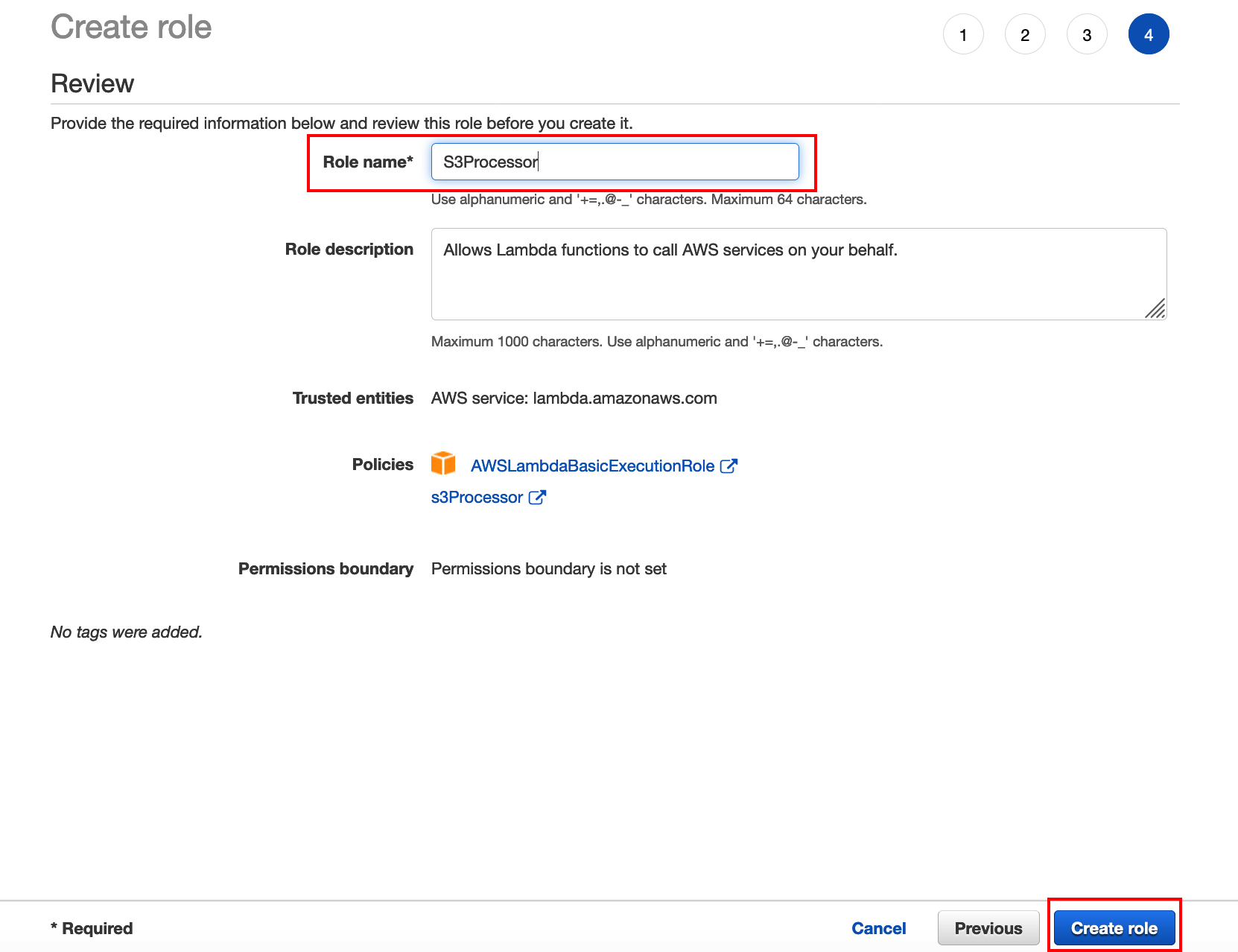
Enter a role name and click Create role.